TL; DR
- Passphrase length is greatest contributor to strength, with memorability is preferable to complexity, but predictability is greatest detractor to strength.
- Dictionary-based attacks use whole words to reduce cycles needed for brute force attacks.
- Add punctuation to turn words into non-words (eg salting) to vault your passphrase to the next level.
Baselining
We have seen that Cloud-backed Password Vaults such as 1Password , LastPass, Dashlane, etc make it easy to store all of our passwords in a single, secure, wallet that is automatically synchronized across all your devices. With these tools we have a method to keep all our passwords in a single place that is secure. The very definition of a High Value Target. Something we must be very diligent in protecting. Where 1Password, et al allow us to use non-predictable, unique, long, and complex passwords in our everyday lives by removing the memorable requirement, the master password for the wallet itself must be memorable.
Let’s review what makes a good master password for your password wallet.
- It must be memorable so we don’t have to write it down for daily use.
- It must be easy to type, since keyboards on mobile devices are harder to use.
- It must be long so that it takes a very, very, very, long time to crack.
- It must be non-predictable so a lucky guess can’t undo all of our hard work.
My own password for my password vault is not a password at all, but an 8-word phrase. It measures between 45 and 60 characters long (I won’t tell you the actual length of course), it is very memorable to me (something I memorized during my elementary school age) so I will never have to write it down. By some measures it’ll take more than one hundred thousand trillion trillion trillion trillion trillion trillion centuries to crack my passphrase. This is all before I applied the technique that I will cover in this blog.
Technique
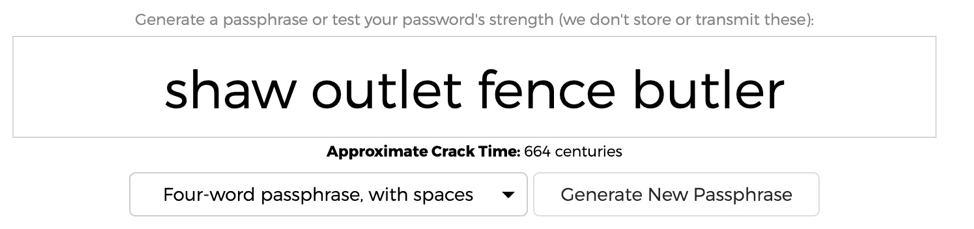
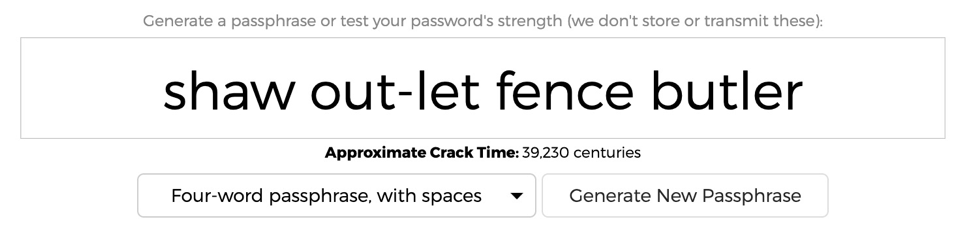
For teaching this technique of salting your passwords, and observe its benefits I will use the cracking algorithm that the site https://useapassphrase.com uses to estimate password strength. When I visited their site, they suggested 4 simple words chosen at random; shaw outlet fence butler. I suggest that you use more than just 4 words for your master passphrase, but let’s step through this simpler phrase.
Our baseline is thus a 4-word passphrase, with spaces, totaling 24 characters in length which is estimated to require 664 centuries to crack. That’s no slouch.
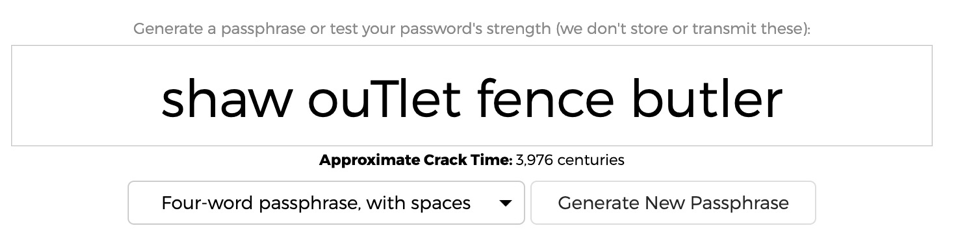
Let’s see what happens if we add a bit of complexity, just a bit. Can we get outsize returns? If we add a capital letter we increase Crack Time by 6x to about 3,900 centuries. Nice.
Okay this is fun. Let’s play with it a bit. What if we swap in a special character?

We get 3.1 million centuries, or 4,674x increase. Awwright! We are starting to get someplace. But maybe we’re getting too carried away. It is harder to crack but not very memorable, so let’s take a step back. Our primary goal for the master password is that it be memorable first, non-predictable and long.
Let’s choose to put the special character at the end. Remembering add a dash at the end can’t be too hard to remember. Does it do anything for us?
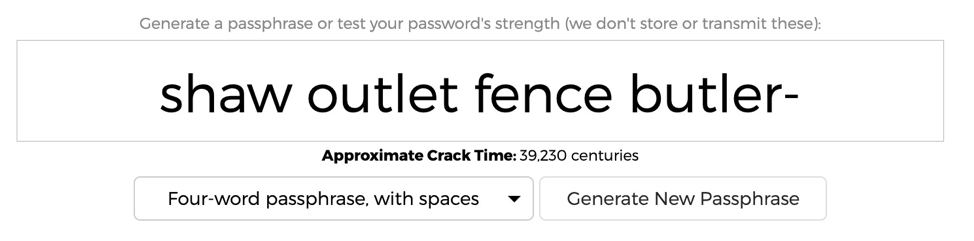
That’s not bad return for a single character. From 664 to 39,230 centuries is a 59x increase in entropy. But moving the special character around doesn’t yield any more entropy gains, as we can easily see below.
That is until we make one of these words, NOT BE A WORD anymore.
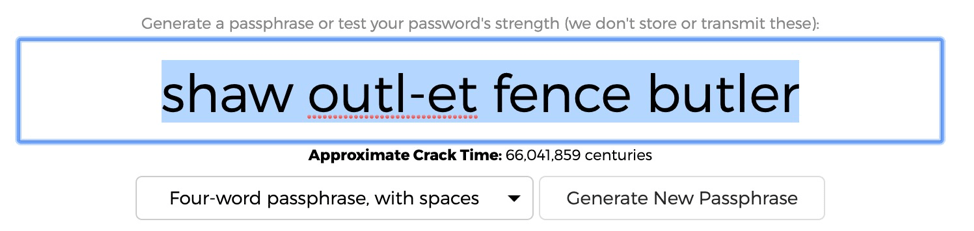
Breaking up the word gives you 66 million centuries or 99460x added entropy over the original length or 1683x over the longer phrase. BINGO! I think we might be onto something. What if make the word into a non-word by deliberate misspelling?

Even if you take back the dash, which reduces both the length and number of dictionaries needed to include in the cracking algorithm but preserve the not a word feature in your passphrase you still get significantly added entropy. 5.2 BILLION centuries or 7,868,692x added entropy on top of passphrase that is considered somewhat strong to begin with.
Conclusion
In short, use words for your memorable passphrases, but if you want to be super-duper extra mega, you will salt your password by throwing a mispelling [sic] in for good measure. The passphrase you would remember is shaw misspelled outlet fence and butler which is not all that much more to remember for a ciritical [sic] password as the password for all the others